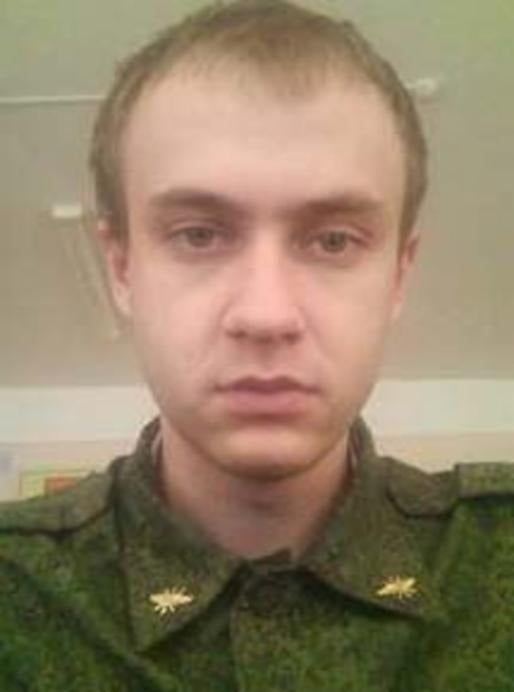
The person at the center of this case
Pavel Valeryevich Frolov (Defendant/Fugitive)
PAVEL VALERYEVICH FROLOV
Justice for Pavel Valeryevich Frolov (Defendant/Fugitive) — the trail went cold in 2020, but the truth hasn't.
Start here
Key leads to think about
What is Frolov's current whereabouts and is he still operating from Moscow or has he relocated?
What specific NotPetya malware variants did Frolov develop or deploy, and can forensic analysis link him directly to the code?
Which specific critical infrastructure systems in Ukraine, France, and Georgia were compromised by Frolov's unit, and what damage resulted?
On October 15, 2020, a federal grand jury indicted Pavel Valeryevich Frolov, a Russian military intelligence officer assigned to Unit 74455, for his alleged role in a sophisticated computer hacking conspiracy targeting critical infrastructure, political campaigns, and international victims worldwide. The conspiracy involved deploying destructive malware including NotPetya, compromising systems in Ukraine, France, Georgia, and affecting the 2018 Winter Olympic Games investigations. Frolov remains at large, last known to be in Moscow, Russia, and the case remains open as federal authorities continue efforts to locate and apprehend him.
Try asking
Claim this imported case
A one-time $10 claim transfers this imported case workspace to your account. You get 10 uploads for this case, 25 daily AI questions for this case, and public tips with files route to you.
This does not start a subscription. When the included limits are reached, the Personal plan unlocks more workspace capacity.
More leads to consider
Beyond the top three above — each detail below could be the thread that pulls this case open.
What communications or financial records exist that connect Frolov to Unit 74455 and Russian military intelligence operations?
Have information about any of these leads?
Even the smallest detail could be the key to solving this case.
Official wording
Source Narrative
Conspiracy to Commit an Offense Against the United States; False Registration of a Domain Name; Conspiracy to Commit Wire Fraud; Wire Fraud; Intentional Damage to Protected Computers; Aggravated Identity Theft Caution: On October 15, 2020, a federal grand jury sitting in the Western District of Pennsylvania returned an indictment against six Russian military intelligence officers for their alleged roles in targeting and compromising computer systems worldwide, including those relating to critical infrastructure in Ukraine, a political campaign in France, and the country of Georgia; international victims of the “NotPetya” malware attacks (including critical infrastructure providers); and international victims associated with the 2018 Winter Olympic Games and investigations of nerve agent attacks that have been publicly attributed to the Russian government. The indictment charges the defendants, Pavel Valeryevich Frolov, Yuriy Sergeyevich Andrienko , Sergey Vladimirovich Detistov , Anatoliy Sergeyevich Kovalev , Artem Valeryevich Ochichenko , and Petr Nikolayevich Pliskin , with a computer hacking conspiracy intended to deploy destructive malware and take other disruptive actions, for the strategic benefit of Russia, through unauthorized access to victims’ computers.
The indictment also charges these defendants with false registration of a domain name, conspiracy to commit wire fraud, wire fraud, intentional damage to protected computers, aggravated identity theft, and aiding and abetting those crimes. The United States District Court for the Western District of Pennsylvania issued a federal arrest warrant for Pavel Valeryevich Frolov upon the grand jury’s return of the indictment.
Remarks: Frolov is alleged to have been a Russian military intelligence officer, assigned to Unit 74455. He was last known to be located in Moscow, Russia.
Timeline of Events
Federal Grand Jury Indictment
A federal grand jury in the Western District of Pennsylvania returned an indictment against Pavel Valeryevich Frolov and five co-conspirators for computer hacking conspiracy, malware deployment, wire fraud, and identity theft targeting critical infrastructure and international victims.