The person at the center of this case
Multiple ransomware victims (businesses and organizations)
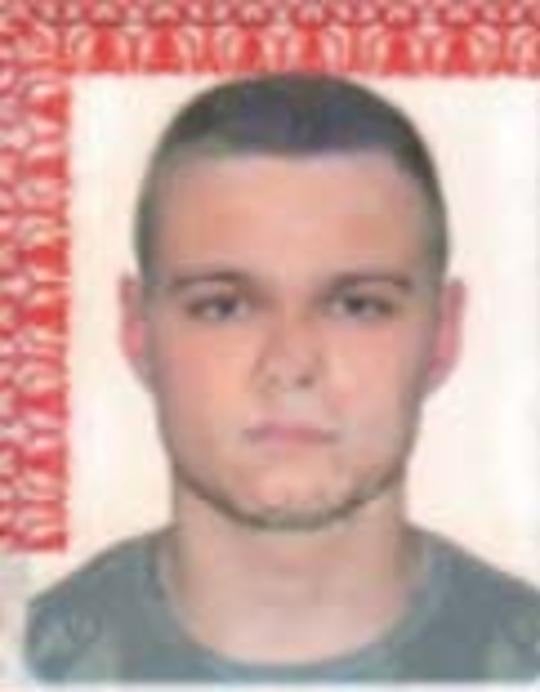
YEVGENIY IGOREVICH POLYANIN
Justice for Multiple ransomware victims (businesses and organizations) — the trail went cold in 2026, but the truth hasn't.
Start here
Key leads to think about
What is Polyanin's current location and is he still actively conducting ransomware operations from Russia?
How many victims has Polyanin targeted and what is the total financial impact of his ransomware campaigns?
Who are the other Sodinokibi/REvil affiliates working with Polyanin and what are their roles in the conspiracy?
Yevgeniy Igorevich Polyanin is wanted by the FBI for orchestrating sophisticated ransomware attacks using Sodinokibi and REvil malware, extorting victims by encrypting their files and demanding payment in virtual currency. He allegedly laundered proceeds from these attacks and threatened to sell stolen data if victims refused to pay ransom demands. Polyanin is believed to be hiding in Russia, possibly in Barnaul, and remains at large as authorities seek information on his whereabouts and criminal network.
Try asking
Claim this imported case
A one-time $10 claim transfers this imported case workspace to your account. You get 10 uploads for this case, 25 daily AI questions for this case, and public tips with files route to you.
This does not start a subscription. When the included limits are reached, the Personal plan unlocks more workspace capacity.
More leads to consider
Beyond the top three above — each detail below could be the thread that pulls this case open.
What cryptocurrency wallets and payment addresses were used to receive ransom payments from victims?
Have information about any of these leads?
Even the smallest detail could be the key to solving this case.
Official wording
Source Narrative
Conspiracy to Commit Fraud and Related Activity in Connection with Computers; Intentional Damage to a Protected Computer; Conspiracy to Commit Money Laundering Caution: Yevgeniy Igorevich Polyanin is wanted for his alleged involvement in ransomware attacks and money laundering activities. It is alleged that, through the use and deployment of Sodinokibi and REvil ransomware, Polyanin left electronic notes in the form of a text file on victims’ computers.
The notes included web addresses for the victims to visit and have their files decrypted. Upon visiting these web addresses, victims were given the ransom amount demanded and provided a virtual currency address to use to pay the ransom.
If a victim paid the ransom amount, Polyanin provided the decryption key, and the victims then were able to access their files. If a victim did not pay the ransom, Polyanin typically posted the victims’ exfiltrated data or claimed he sold the exfiltrated data to third parties.
Polyanin has been charged in an indictment filed in the United States District Court for the Northern District of Texas, Dallas, Texas, with conspiracy to commit fraud and related activity in connection with computers, substantive counts of intentional damage to protected computers, and conspiracy to commit money laundering. Remarks: Polyanin is believed to be in Russia, possibly in Barnaul, and is one of many Sodinokibi/REvil ransomware affiliates.
Timeline of Events
Sodinokibi/REvil Ransomware Deployment
Polyanin deployed ransomware that encrypted victims' files and left electronic notes with ransom demands and cryptocurrency payment instructions
Data Exfiltration and Threats
Victims' data was exfiltrated; Polyanin threatened to post or sell stolen data if ransom was not paid
Federal Indictment Filed
Polyanin charged in U.S. District Court for the Northern District of Texas with conspiracy to commit fraud, intentional damage to protected computers, and conspiracy to commit money laundering